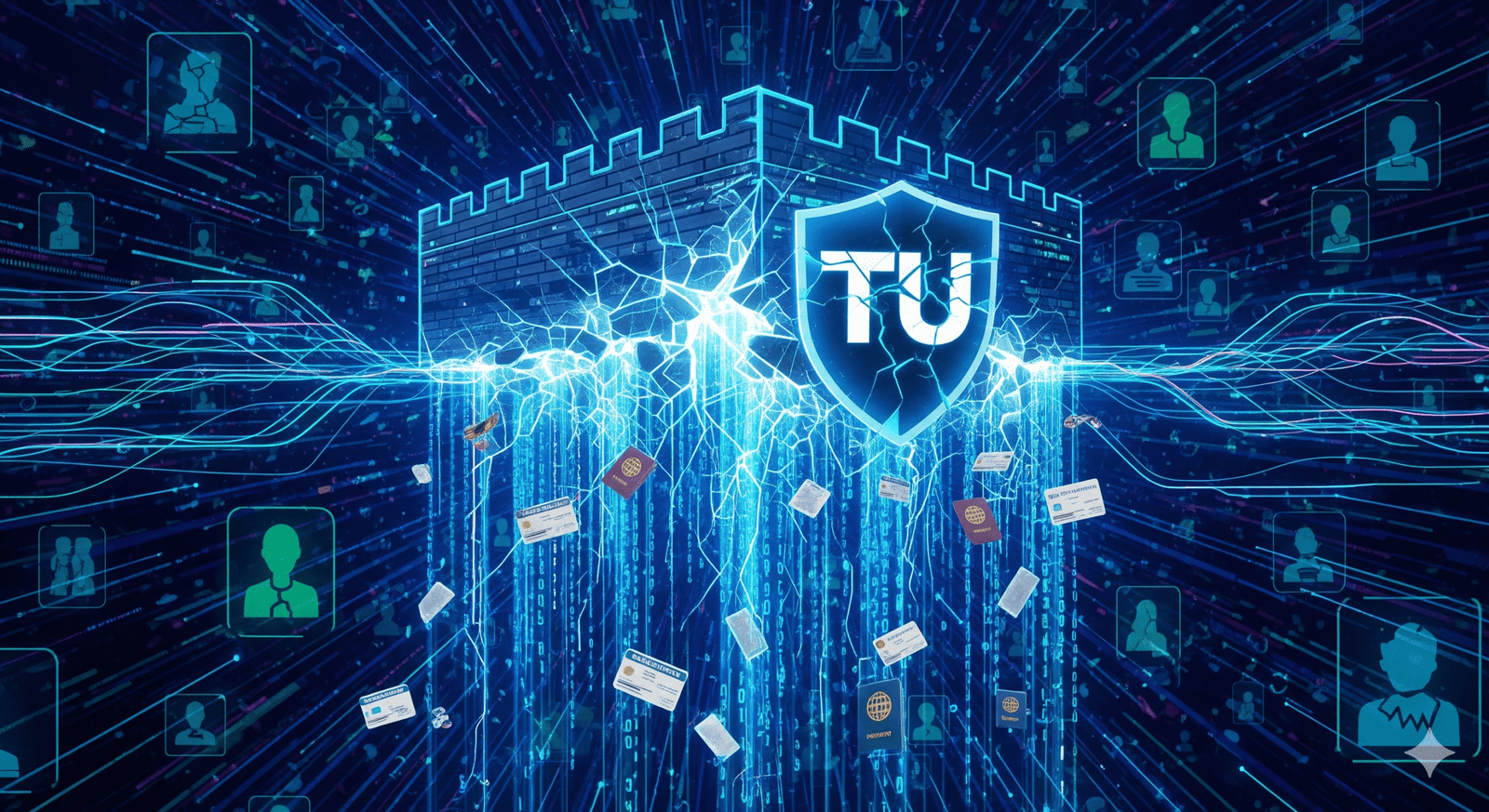
In a digital age where personal data is the new gold, the recent news of a hack at credit reporting giant TransUnion sends a chilling reminder of our collective vulnerability. The breach, which exposed the personal information of over 4.4 million Americans, is a stark illustration of the escalating risks posed by sophisticated cybercriminals and the often-overlooked vulnerabilities of third-party vendors. While TransUnion has assured the public that its core credit databases were not compromised, the theft of sensitive data like Social Security numbers and birth dates for millions of people is a serious incident with potentially long-lasting consequences for victims. This event is not an anomaly but rather the latest in a troubling series of high-profile data breaches, underscoring a systemic failure to adequately protect consumer information.
The details of the hack are particularly illuminating. TransUnion has stated the breach originated from a “third-party application” used for consumer support operations. This highlights a critical, and often weakest, link in the cybersecurity chain: the network of vendors and partners that a company relies on. In the pursuit of efficiency and outsourcing, companies grant access to their systems and, by extension, their data to external entities. If one of these vendors has a security vulnerability—whether it’s a software flaw, a weak password, or a successful social engineering attack—it can become an open door for hackers to a company’s sensitive data. In this case, reports from cybersecurity firms and law firms suggest a possible connection to a broader wave of attacks targeting Salesforce-hosted databases. This vector of attack, where hackers use social engineering to trick employees into granting access to third-party applications, is a growing and dangerous trend.
For the 4.4 million affected individuals, the implications are severe. While TransUnion has said no credit information was accessed, the exposed data—including names, addresses, phone numbers, birth dates, and in some cases, Social Security numbers—is a treasure trove for identity thieves. This information can be used to open fraudulent credit accounts, file for tax refunds, or even commit medical identity theft. The company has offered two years of free credit monitoring, but this is often seen as a minimal measure. Experts and consumer advocates argue that the damage from a data breach can last a lifetime, and two years of monitoring is a temporary bandage on a permanent wound. The psychological toll is also significant, as victims must live with the constant fear that their identity could be compromised at any moment.
This incident also brings into question the regulatory and ethical responsibilities of data-holding companies. As a credit bureau, TransUnion is one of a handful of companies that act as custodians of America’s financial identities. The public trusts them to be secure, and when that trust is broken, it raises questions about accountability. The fact that TransUnion only disclosed the breach more than a month after it occurred—it happened on July 28 and was disclosed on August 28—may have violated state and federal laws and gave criminals a significant head start. This delay, combined with the lack of transparency about the specific third-party vendor or the full scope of the exposed data, is a recurring theme in major breaches and erodes consumer confidence further.
The TransUnion hack is a grim wake-up call. It’s not just a story about technology; it’s a story about trust, responsibility, and the perilous reality of a hyper-connected world. It is a powerful reminder that in the fight against cybercrime, a company’s defenses are only as strong as its weakest link, and for millions of consumers, that link may have just been a third-party application they had never heard of.
21 Bullet Points on the TransUnion Data Breach
Date: August 29, 2025
- TransUnion, a major credit reporting agency, has confirmed a significant data breach.
- The breach exposed the personal data of over 4.4 million American consumers.
- The hack was discovered on July 30, but the unauthorized access began on July 28.
- TransUnion disclosed the incident to regulators and the public approximately one month after discovery.
- The breach originated from a cyber incident involving a “third-party application.”
- This application was used for TransUnion’s U.S. consumer support operations.
- The company stated that no “credit information” or “core credit database” was compromised.
- However, sensitive personal information was exposed.
- Exposed data includes names, Social Security numbers, dates of birth, addresses, and phone numbers.
- The specific third-party vendor involved has not been publicly named by TransUnion.
- Cybersecurity experts and media reports suggest a potential link to a widespread campaign targeting Salesforce-hosted databases.
- The attack method likely involved social engineering to trick employees.
- The stolen data is a treasure trove for identity thieves and fraudsters.
- TransUnion is offering affected individuals 24 months of free credit monitoring through its own service, myTrueIdentity.
- This breach adds to a history of cybersecurity incidents at TransUnion, including a 2022 breach in South Africa.
- Consumer rights law firms have begun investigating potential class-action lawsuits.
- Critics argue that the two years of credit monitoring are an inadequate response to the potential for a lifetime of identity theft.
- The delayed public notification may have given hackers a significant head start in using the stolen data.
- This incident highlights the significant security risks associated with third-party software dependencies.
- It raises serious questions about the accountability of companies that act as custodians of vast amounts of consumer data.
- The breach is a reminder that even major financial institutions can be vulnerable to sophisticated and evolving cyber threats.
Separate Answer: When, Where, Why, and Who
When: The unauthorized access occurred on July 28, 2025. The breach was discovered two days later, on July 30, but was not publicly disclosed until August 28, 2025.
Where: The breach occurred in the United States, originating from a third-party application used for TransUnion’s U.S. consumer support operations.
Why: The hack was a result of unauthorized access gained through a vulnerability in a third-party application. While TransUnion did not disclose the specifics, cybersecurity experts believe it is part of a larger, ongoing social engineering campaign targeting companies that use Salesforce.
Who: The hack was perpetrated by unidentified cybercriminals. The victims are over 4.4 million U.S. consumers whose personal information, including names, birth dates, and Social Security numbers, was exposed. TransUnion, as the company responsible for the breached data, is now facing legal and public scrutiny.